Protect branch floors, vaults, and employees without mass surveillance. Real-time threat and victim identification at every physical access point.
Traditional CCTV records continuous high-resolution footage—creating mountains of stored video that becomes a surveillance liability, not a security asset. A server breach exposes decades of employee and customer footage. But even with perfect footage, CCTV delivers zero proactive intelligence.
Criminal networks walk through front doors undetected. Employees arrested between annual background checks retain vault and data center access for months. Organized check fraud rings conduct coordinated intrusions at multiple branches simultaneously while bank staff has no way to identify them in real time.
Safience collapses this blind spot. We deliver real-time, threat-specific identification at the exact moments criminals, insiders, and at-risk persons are physically present—without surveillance, without footage, without mass storage liability.
Each product serves a distinct role in the physical banking security ecosystem. Together, they collapse decades of disconnected criminal justice data into real-time, location-specific identity intelligence.
Organized fraud rings, money mule networks, and trafficking victims enter through the lobby every day. Traditional CCTV cannot identify them. Safience does—before they reach a teller window.
Traditional CCTV only records. It cannot identify who is entering the branch or whether they belong to a known fraud ring. By the time a teller processes a fraudulent check, the perpetrator is already gone and other branches have been hit.
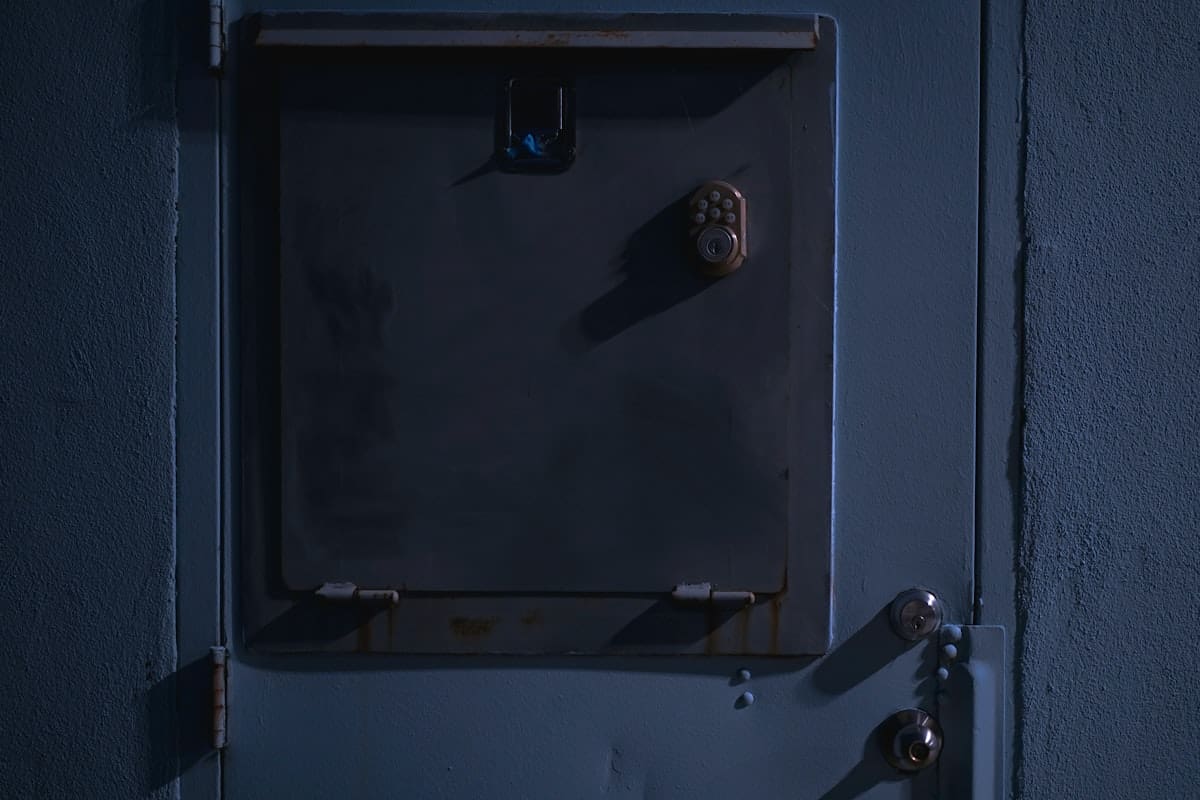
RTIS sensors capture a single ephemeral <100KB facial crop at the branch entry door. If the person matches a known organized fraud ring member in UMbRA, a silent alert is routed to branch staff before they approach a teller window.
Banks have zero ability to identify trafficking victims or missing persons entering their facilities. A victim may walk into a branch to deposit cash or open an account, but staff has no way to recognize them or intervene without putting the victim at further risk.
RVIS sensors at urban branches and ATMs cross-reference live captures against trafficking and missing person records 24/7. A match triggers mandatory human review at the Safience Rapid Action Center and coordinated intervention with law enforcement.
Credential-based access control leaves massive blind spots. Stolen badges, shared PINs, and compromised credentials grant physical access to the crown jewels. Biological identity verification closes these vulnerabilities.
Card credentials and PINs can be stolen, shared, or cloned. A badge grants access; it doesn’t verify the person holding it is authorized to use it. Only biological identity verification closes this vulnerability.
RTIS sensors verify the physical person matches the credential AND simultaneously checks UMbRA for disqualifying criminal records or warrant status. No more shared PINs, stolen badges, or credential proxy attacks. Every vault access is biologically verified.
Terminated employees and suspended contractors retain physical access until manual deprovisioning, which can take days or weeks. IT systems are slow; badge readers don’t deactivate immediately; facility managers lack real-time visibility.
RTIS enables a private, localized ban list residing only on the bank’s owned sensors—zero external network exposure. Deprovisioning is immediate and auditable; no gaps between termination and access revocation.
Annual background checks leave massive blind spots. An employee arrested between review cycles stays undetected for months. Continuous, consent-based monitoring closes the gap with zero false positives.
Traditional monitoring relies on text-based name matching, resulting in crippling false positives for common names. Annual checks leave a massive blind spot—an employee arrested between review cycles stays undetected. Vault staff, wire handlers, and PII-access employees pose ongoing risk.
FCRA-compliant, consent-based continuous monitoring. New arrests trigger an alert ONLY if there is a confirmed facial match. Zero false positives. Protects wire access, vault, and PII-handling staff with auditable, up-to-the-minute coverage. Integration with physical access systems enables immediate suspension pending investigation.
Banks struggle to prove continuous risk mitigation to underwriters. Point-in-time assessments don’t satisfy modern insurance requirements. Fidelity policies and commercial crime bonds remain expensive because the bank cannot demonstrate ongoing, auditable security posture.
Combining eMotive (insider threats), RTIS (physical breach detection), and UMbRA (transaction screening) creates an irrefutable, auditable data layer for direct premium negotiations on fidelity policies and commercial crime bonds. Real-time risk metrics reduce underwriter concern and justify lower rates.
From edge capture to legally defensible action in under 60 seconds.
Safience is incapable of mass surveillance by design. Our edge sensors capture a single sub-100KB still image at the moment of identity decision. Non-matches are purged instantly. Nothing is stored on the device. There is no video footage, no forensic rewind, no live monitoring capability, and no surveillance liability.
Physical security addresses threats present at branch locations. But threats also move through digital channels—account opening, transactions, wire transfers. Synthetic identities, money mule networks, and compliance gaps enter before anyone walks through the front door.
See how Safience secures every digital entry point with 5 targeted use cases.
